
SecLint: An Agentic Code Vulnerability Scanner
Context-Aware, Agent-Driven Security Scanning That Scales Beyond Manual Reviews
SecLint addresses a critical gap in code security by combining manual review rigor with automated analysis speed. Traditional approaches — manual reviews are slow, error-prone, and don't scale, while rule-based static analyzers (SAST) produce generic alerts and false positives without contextual understanding.
What is SecLint?
A Python-based AI agent leveraging retrieval-augmented generation (RAG) to detect insecure code patterns. The tool grounds language models in security best practices by retrieving relevant guidance before analysis, then generating remediation steps based on both code context and established practices using the ReAct pattern.
Technical Architecture
Pipeline Overview

Key Components
Directory Watching (Watchdog): Monitors target folders and triggers analysis when .py files are saved, enabling real-time scanning configured via config.yaml.
AST-Based Chunking: Python's ast.parse converts code into Abstract Syntax Trees, isolating functions, classes, and statements while preserving logical flow without executing code.
Knowledge Base (ChromaDB + OWASP): Builds local RAG databases from OWASP secure coding guidelines, with documents embedded via OpenAI's embeddings API for semantic search during analysis.
Contextual LLM Analysis: LangChain orchestrates GPT-4/o4-mini-high calls, enabling the agent to summarize code context, retrieve relevant security rules, and generate detailed JSON-formatted remediation steps.
Output Report: Generates structured console reports listing context descriptions, severity levels, best practices, and actionable recommendations per code snippet.
Performance Comparison
Flask Debug Mode Example
SecLint Output:
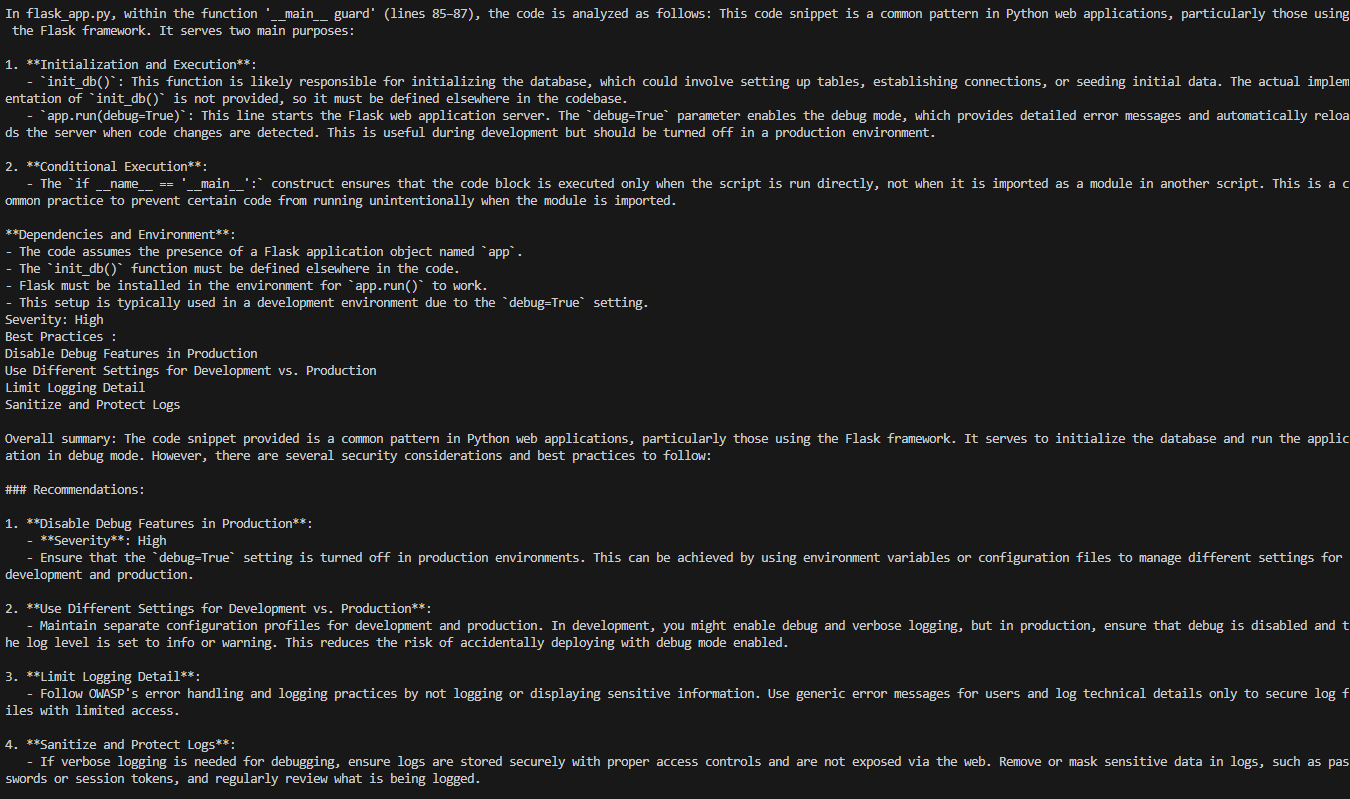
When analyzing app.run(debug=True), SecLint examines the __main__ block context, retrieves OWASP best practices regarding production debug modes, and synthesizes four actionable remediation steps with severity labels.
Bandit Output:

By contrast, Bandit flags issue B201 with severity/confidence notes and references CWE-94 without contextual explanation.
Access Control Example
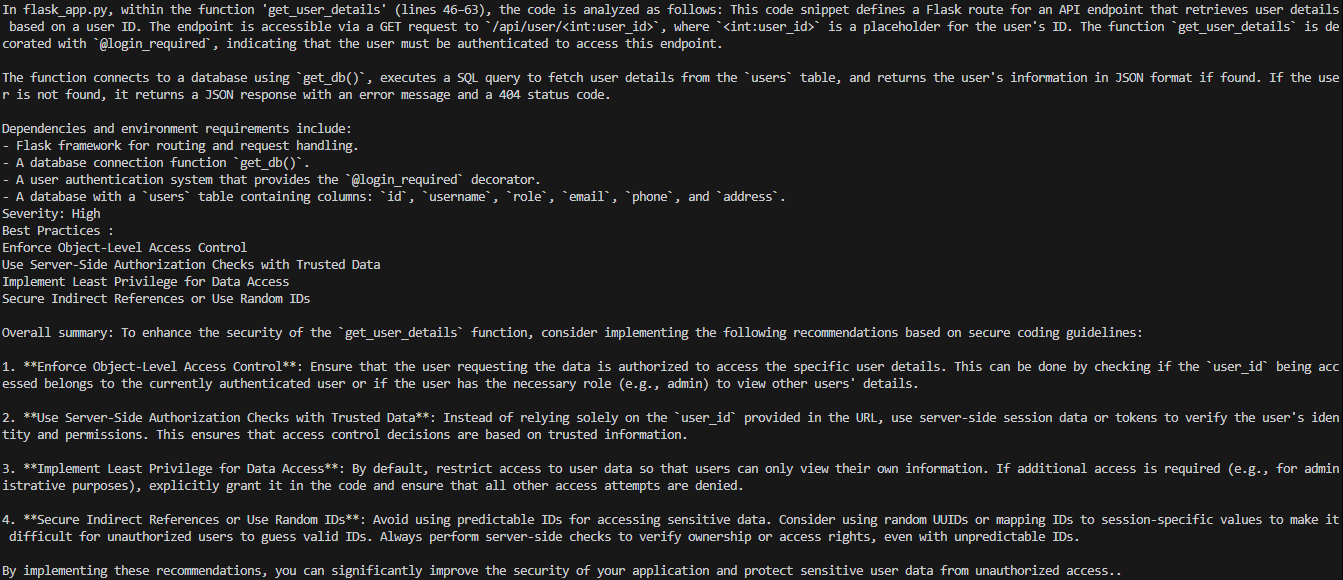
SecLint detects missing object-level access control in the get_user_details endpoint, warning that authenticated users can retrieve arbitrary records. Recommendations include server-side authorization checks, least-privilege access, and indirect references. Bandit produces no warning for this logic flaw.
Key Advantages
SecLint reasons about code contextually rather than pattern-matching blindly. Unlike traditional SAST tools, it explains vulnerability causes and remediation approaches, not just flagging issues. This contextual guidance proves substantially richer than generic static checker warnings.
Future Development
Planned enhancements include:
- SAST Integration: Combining deterministic and AI-driven approaches
- Multi-Language Support: Extending beyond Python to JavaScript, Java, Go
- CI/CD Hooks: Integrating into build pipelines with pull request comments
- Knowledge Base Expansion: Adding SANS, CERT guidelines, and custom corpora
- Prompt Refinement: Using DSPy frameworks for iterative improvement
Conclusion
SecLint demonstrates how RAG pipelines improve vulnerability detection by grounding AI analysis in authoritative best practices. By combining Watchdog, Python AST parsing, OpenAI embeddings, ChromaDB, and LangChain-driven agents, the tool provides context-aware security feedback exceeding traditional rule-based approaches.
GitHub: github.com/Har1sh-k/SecLint
Thanks to Anshuman Bhartiya and Avradeep Bhattacharya for conceptual guidance.